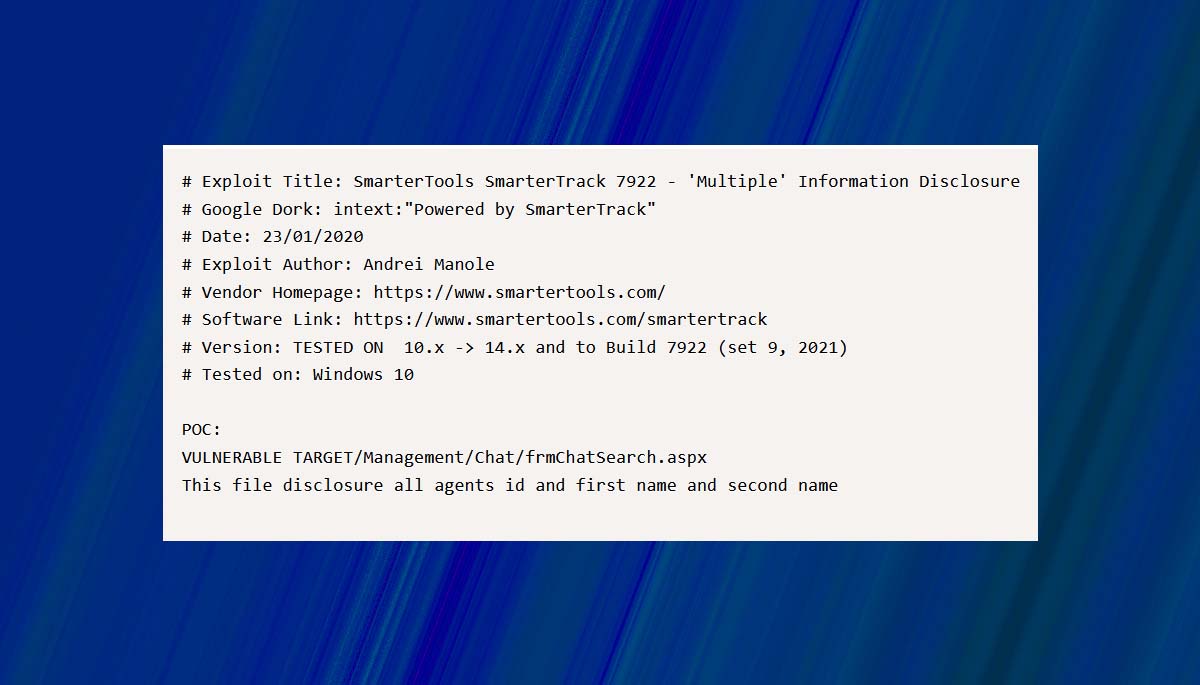
To hack a website hackers use different tricks and “intext:””powered by smartertrack””” is one of them which targets the TARGET/Management/Chat/frmChatSearch.aspx so hackers can easily find out the the agents id and first name and second name.
Those who are not aware of what is smartertrack? I would like to highlight that, it is on-premises help desk software that allows businesses to deliver unparalleled customer service.
If you will explore this product in deep then you will find out that, it is include a ticketing generate system, live chat support, call logging and phone system integration (whatsapp call, telegram), knowledge base articles for quick help, news items, and a place where customers can interact with each other as well as with the business.
You can check more about this here:
- https://www.smartertools.com/smartertrack/help-desk-software-overview
As this ticket generate + chat support system works well on both desktop or mobile and a lot of people prefer it to share business details and other sensitive data. Hackers keep an eye on all important information so they can get details of employee or businessman to steal the possible leads, quotes, etc.
That’s why they use “intext:””powered by smartertrack””” trick to extract the agents’ id and first name, second name and phone number.
So if you are using it (or the version is too old) then we advice, update Smartertrack help desk software and save your sensitive data from the hacking and don’t forget to share it with others.